Nursing Essay Services – Best Online Nursing Papers
Writing essays is a common prerequisite for nursing programs today. No matter what level of nursing education you’re pursuing, a BSN, MSN capstone, or DNP, this is always true.
Having a well-written nursing essay paper to turn in is crucial because it will serve as the basis for how well you do in the entire course.
It takes hard work and careful attention to detail to excel in a nursing course. Nursing assignments should be used to demonstrate these abilities. That’s why we offer high-quality nursing essay writing help to our clients. In order to get a great grade, you need to choose nursing essay services that are familiar with the standards of the nursing field.
As your learning partner, we recognize that a number of variables affect your academic success. Stress from work or family responsibilities, or simply being too tired to do anything worthwhile, all fit into this category.
You can rely on our nursing essay services to assist you in this endeavor. To provide these services, we have recruited professionals that are both capable and knowledgeable.
Whether you need assistance with a nursing essay, research paper, dissertation, or term paper, we can write it for you. We have been helping students for quite some time now, so you can rest assured that the nursing papers you receive from us will be of the highest quality.
When you hire us to write your nursing essay, you can be sure that you will get a high-quality paper that follows all of your specific instructions.

Our Nursing Essay Services Writers will Help you with:
- BSN, MSN, or DNP essay paper or project;
- Nursing research proposal;
- PICO (Population, Intervention, Comparison or Condition, Outcome) question or statement;
- Evidence-Based Practice (EBP) Proposal;
- and any other nursing paper you need.
Get Help from Our Nursing Essay Services
We offer help with essay projects for any nursing topic at any academic level. The essay services for nursing we provide include:
- Nursing writing services. We’ll help you to write your paper from scratch, just provide us with the idea or topic and all the requirements. Our writers are well-qualified and have plenty of experience in academic writing so they know all the drills.
- Paraphrasing service. Want to make your writing unique and engaging? Our team will breathe new life into your paper! With the help of top paraphrasing techniques and natural creativity, our writers can do miracles!
- Editing service. Applying the proper format, following the right style and requirements…that takes a lot of time and skills, doesn’t it? Well, our service can take the burden of editing off your shoulders!
- Proofreading service. There’s no place for errors in academic writing! Entrust our writers to eliminate every single mistake and make your paper the best it can be.
- Formatting service. The format for academic writing is like an endless spider web with too many requirements and details. But we can untangle this problem together in no time!
The Ordering Process Explained
Simply follow these FOUR easy steps to place an order. Our writers and editing team will ensure you receive what you require.



Our Professional Writers
Essay Writing help is not something that can be provided by just anyone; can a general writer provide support with a highly technical nursing project? The answer is of course that the help that you need must come from an expert in your field which is why through us you will always get to work with an expert:
- We have an amazing team of writers and editors. All of them have many years of experience writing academic essays and can help you with your project.
- Our skilled writers are specialized in different subjects. This allows us to be able to help you write your project on a wide range of academic courses. We will only match your project with a writer holding a degree certificate relevant to your essay.
- Thanks to our expert team, we can help you write, edit, and proofread your nursing project. Each service is carried out by experts in that area.
- Relevant degree within a subject related to your nursing writing and is handling PhD-level requests we have
- We also provide formatting services to help you use the adequate format for your project. Our professionals are aware of the different requirements that need to be included in your paper.
- Our expert team will do additional research following your requirements to ensure your project is perfect.
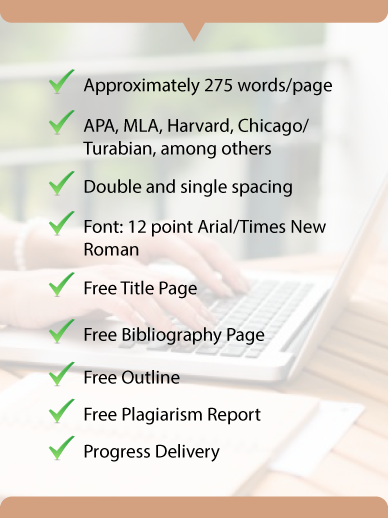
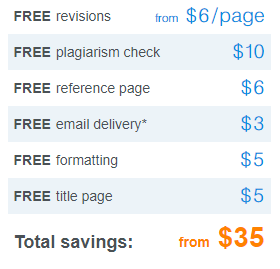
Formats and Features
Nursing Essay Writing Services
Every part of the nursing paper is important. Starting with the selection of nursing project ideas our company provides a range of services to help you. Services that we provide include:
Testimonials